Ng Chong
August 2012
While security is critical in an ever more interconnected world, security tends to be perceived as overbearing and inconvenient for the user. This along with mobility has prompted a growing number of users in UNU interested in bringing their own devices to work, which in turn has created a demand to access enterprise applications and data from multiple devices and locations. These devices are often more powerful and convenient to use than what UNU provides, putting into question the current ICT delivery model in UNU. How can the ICT department respect user preferences and support workforce mobility while fulfilling the institutional responsibility of ensuring security?
Trends that are transforming the landscape of work computing and its delivery model
Nowadays the workforce of an organization is increasingly mobile. The constant need to be connected with people and ICT resources from anywhere is a trend that is here to stay. Enterprise mobility is also benefiting from the rapidly maturing cloud models for on-demand access to applications and infrastructure. At the same time, there is increasing evidence outside and inside of UNU that workers use more than one device to carry out their functions. According to a Forrester Research Report, February 2012, over 50% of information workers use 3 or more devices. This movement is also accompanied by a great diversification of endpoint devices (e.g., smartphones, tablets, etc.) that are available in the marketplace.
Vision
The confluence of these trends fuels the vision of the UNU Flexible Computer Strategy. The framework is predicated on the value of providing a consistent interface to UNU ICT resources, irrespective of device and location. To realize this vision, C3 draws inspiration from the machine and infrastructure abstraction capabilities of virtualization and cloud technologies available in our UNU Data Centers. The implementation rests upon the creative use of these technologies and network safeguards to overcome some of the security challenges that device freedom and mobility pose to the network.
Conceived in 2009, the strategy only began to thrive as a prototype experience rather than a laboratory concept when UNU’s cloud desktop provisioning became a reality in late 2011. The three technology service delivery methods available under the UNU Flexible Computer Strategy are described below.
Delivery Method 1: Access ICT resources and services from your UNU computer
The traditional delivery method continues as an option for users offering flexibility in the choice of operating system and hardware after consultation with C3. Devices are provided with essential applications/tools already installed and new software installations must be approved by C3. While this system is fine for many users and is inherently easier to support, we understand that it may be inadequate to meet the needs of users who want to mirror the same productive software environment s/he uses at home.
Delivery Method 2: Access your UNU computer using any device
Too much security can reverse the benefits of ICT and hinder productivity. On the other hand, with the emergence of increasingly more sophisticated cyberattacks, ICT security is an ever evolving arms race. C3 faces a challenge of striking the balance between maintaining security and preserving the user experience of the device for employees. The Flexible UNU Computer Strategy is a major step in resolving this control and usability paradox. Under this delivery method, your UNU computer is a machine that resides in the cloud or sits on your desk. The latter is best suited for high-end computing such as graphics intensive applications.
A salient characteristic of this method is that it respects user preferences and work styles without weakening the network security. While the UNU computer is securely locked down, you can connect to your UNU computer from any location, both on and off campus, using a personally managed device of your own choosing. Thus, this option gives you the ability to follow your UNU computer everywhere you go with the same experience you get in the office, and allows for better separation of personal data and institutional data.
Delivery Method 3: Direct access to UNU ICT resources and services using any device
Our core ICT services are already remotely accessible and the gap between on-site and off-site user experiences is narrowing. A corollary benefit of this vanishing divergence is that users can consume ICT resources and services without the need of a UNU computer. As ironic as it may sound, bringing this remote capability to the LAN gives rise to yet another option that helps increase user satisfaction while reducing hardware and support costs.
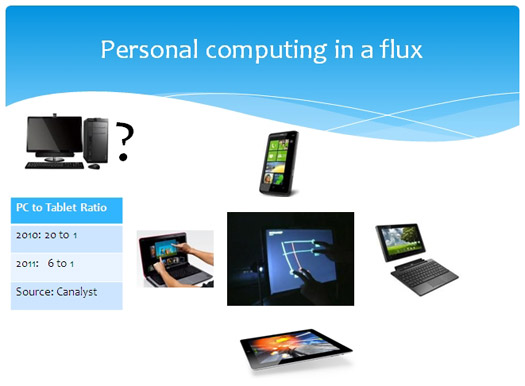
If we take a closer look at what is happening in a typical home environment, it is apparent that users can enjoy and explore a wider range of productivity applications at home than currently possible in UNU. The same is true on the hardware front – the devices that users have tend to be more cutting-edge than what UNU provides, owing in part to the slow refresh cycles of hardware and budgetary constraints in UNU. In fact, it is just impossible to predict what the future of personal computing is like. Rather than committing to a specific type of hardware using a one-size-fits-all approach, it now makes sense to move towards supporting end-user device ownership.
Delivery Methods are not mutually exclusive
As our efforts to blur the line between on-site and off-site access continue, it is conceivable that in future the UNU computer could become redundant, particularly for those users who habitually work from different places. However, even for this type of user, they may still want to connect to their own UNU computer in such situations where certain legacy software applications are not compatible with the device that the user uses to access the UNU resources. Another example where users may find the UNU computer advantageous is when the data that they want to work with are already in the UNU cloud (e.g., sending an email with a file attachment that lives in the UNU file system). In such case, remotely accessing your UNU desktop would be more efficient than the other way around, i.e., downloading data onto a user device.
Bring Your Own Device Policy
This is an evolving strategy – in this early phase, UNU still provides hardware to all by default and C3 helps interested users adapt to using their own PC, Mac, smartphone or tablet for work purposes. These early adopters of ‘Bring Your Own Device’ (BYOD) along with progressive policies including sensible subsidization and a framework that enables users to seamlessly transition their personal devices into work mode can lead to wider user acceptance of BYOD in UNU.
Implementation of this strategy will take the focus off front-end hardware provisioning and allow C3 to devote more resources to infrastructure refinement, enabling improved services delivery and reduced costs. Users benefit from using a device tailored to their own needs, boosting satisfaction and productivity, a win-win proposition for both users and UNU.